Key Changes in Firmware 3.1.0¶
This release introduces important security, configuration, and service changes.
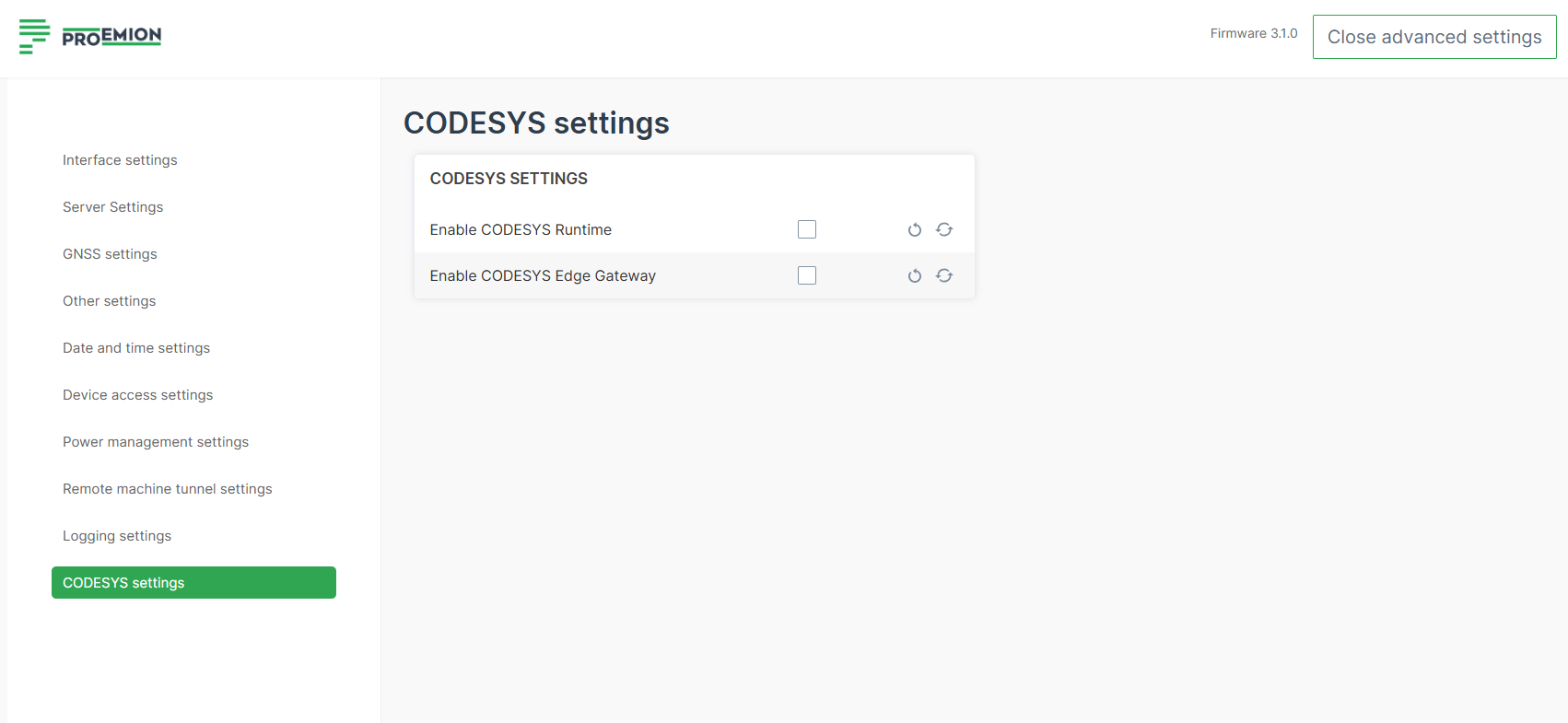
CODESYS Runtime and EdgeGateway Service Configuration¶
To improve device security and minimize unnecessary service exposure, the following changes have been introduced:
Note
Existing CODESYS applications will not run until services are manually re-enabled.
- This is a persistent configuration; future firmware updates will not reset this setting.
- Use COTA with
.clmsettings files for efficient updates. Verify all Wi-Fi profiles to ensure settings are correctly applied.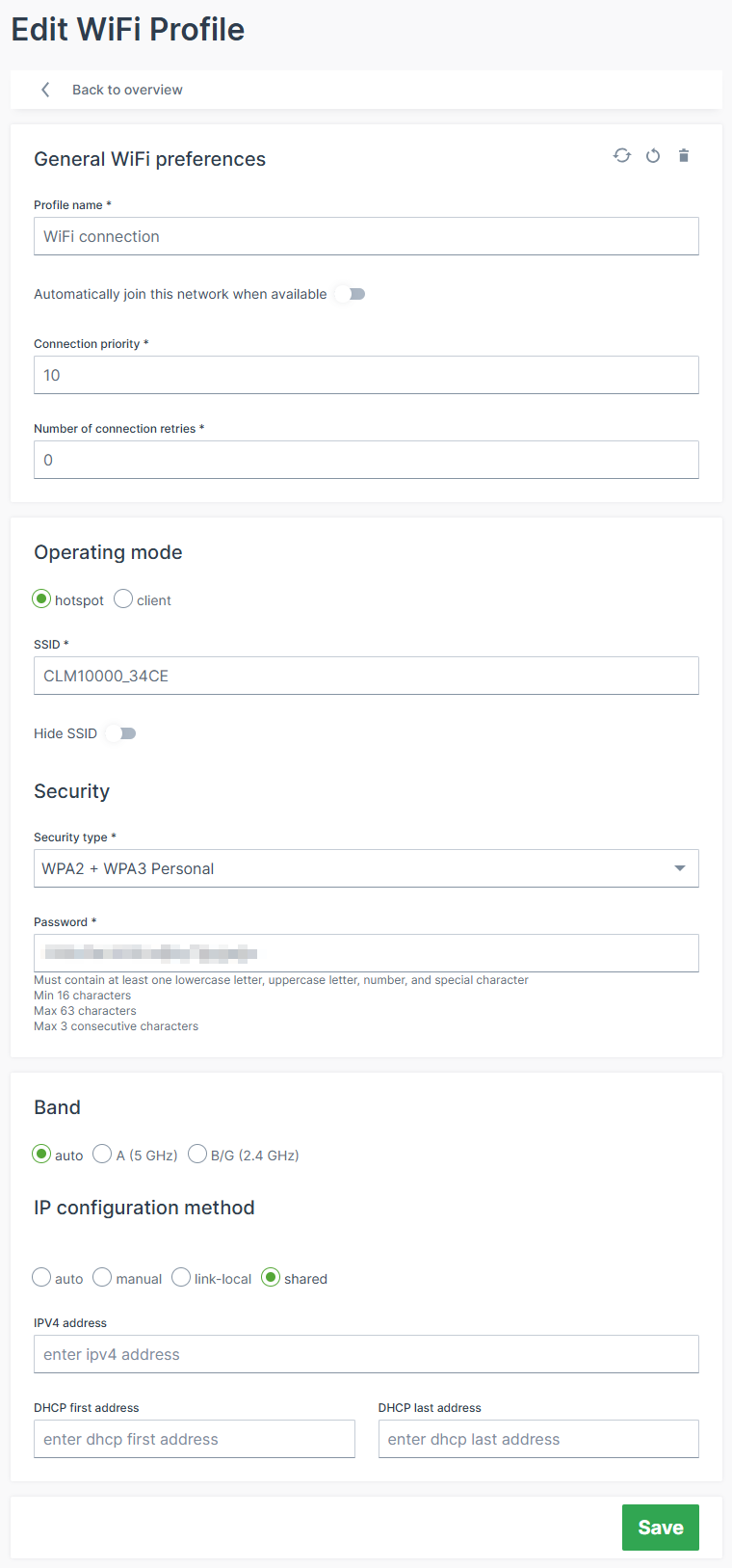
Note
Test changes first on a single device; Hotspot password changes may be necessary.
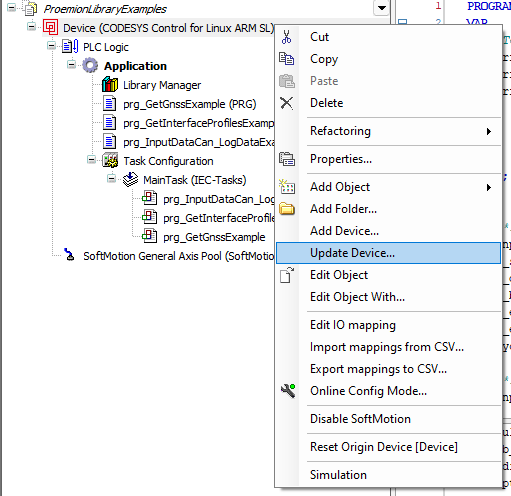
The device description has been updated from version 4.9.0.0 to 4.17.0.0..
You need to download and install the CODESYS Add-on - CODESYS Control for Linux ARM SL version 4.17.0.0 and update your applications. Right-click on the Device (CODESYS Control for Linux ARM SL) and select Update Device from the menu:
Password Policy Update¶
To further enhance device security, passwords for accessing the device will follow a revised and more robust password policy:
- Length: 8–63 characters.
- Must include: one uppercase, one lowercase, one number, one special character.
- A maximum of 3 identical consecutive characters is allowed.
Note
Wi-Fi Pre-Shared Key (PSK) for client mode is not affected by this change to maintain compatibility with certain legacy devices.
Wi-Fi Security and Operating Mode Changes¶
To align with modern security standards and ensure reliable wireless communication, several outdated or less secure Wi-Fi modes have been removed from the available configuration options.
- Removed insecure or deprecated modes:
- Open (unencrypted) networks
- OWE (Opportunistic Wireless Encryption)
- WPA2 + WPA3 Enterprise (combined mode)
- Wi-Fi ad-hoc mode is removed.
- Existing configurations using these modes will remain functional temporarily, but the corresponding settings will be marked as deprecated.
- Firmware enforcement:
- Deprecated Wi-Fi security modes rejected from firmware versions ≥ 2.0.0
- Ad-hoc mode rejected from firmware versions ≥ 3.0.0
- Future support for WPA2 + WPA3 Enterprise may be reintroduced on request with a defined setup.
SSH Service Behavior¶
To enhance device security and reduce potential attack surfaces, the SSH service is no longer active in the factory default configuration.
- SSH is disabled by default on newly produced devices.
- Users can manually enable the SSH service on demand when remote access is required.
- Activation requires uploading a public key via the JSON API SSH endpoint.
This change ensures that SSH access is only available to authorized users and initiated through a secure key-based authentication process.